Cyber Alert - Ongoing Phishing Campaign Impersonating FINRA Employees
Impact: All Firms
Member firms should be aware of an ongoing phishing campaign that involves fraudulent emails purporting to be from FINRA employees. The goal of the threat actor is to trick the recipient into replying and participating in a Microsoft Teams call. Anyone who receives these fraudulent emails should delete them and consider blocking the domains from which they were sent.
This Alert describes the campaign and includes recommendations to help firms identify the fraudulent emails and mitigate the threat.
Background
Beginning as early as March 26, 2026, a new email phishing campaign has been targeting broker-dealers. Bad actors purporting to be FINRA employees are attempting to coerce recipients into replying to an email message claiming to be “a time-sensitive matter relevant to your firm’s regulatory environment.” Member firms should use caution when replying to emails from unknown email domains and never open attachments or click on links from suspicious domains, as they can contain malware or be designed to steal login credentials and other information. Additionally, for awareness, similar campaigns are currently targeting SIPC- and SEC-regulated entities as well as the New York Department of Financial Services.
The campaign includes emails originating from the domains “finra[.]org[.]getencryvia[.]com” and “finra[.]org[.]myencryvia[.]com” (brackets added to prevent accidental clicks) and subject lines containing a member firm’s name. The message asks the recipient to reply to the message and set up a Microsoft Teams call with the threat actor. The signature block includes the words “Member Services,” along with FINRA’s name and a Washington, D.C., address.
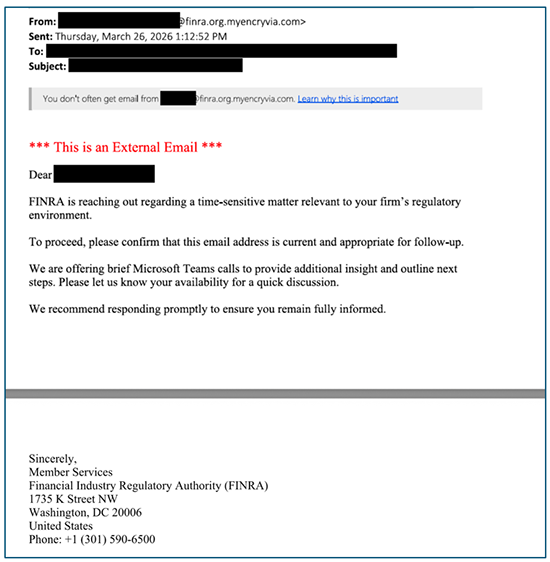
As a reminder, legitimate FINRA emails will only be sent from the “finra.org” domain. Member firms should delete such fraudulent emails and consider blocking the fraudulent domains (“finra[.]org[.]getencryvia[.]com” and “finra[.]org[.]myencryvia[.]com”).
Recommendations to Protect Your Firm
To protect against this email phishing campaign, FINRA recommends member firms:
- alert technology staff to the following indicators of compromise:
- finra[.]org[.]getencryvia[.]com
- finra[.]org[.]myencryvia[.]com
- block emails from these fraudulent domains at the network level and instruct users to delete any that reach their inboxes;
- consider blocking the fraudulent domains at your firewall;
- monitor network traffic for activity related to these domains; and
- remain vigilant for variations of this phishing campaign, including changes in:
- sender names, subdomains and domains;
- email content and subject lines;
- file names and attachments; and
- suspicious hyperlinks (e.g., misspellings or unfamiliar domains) contained within emails.
FINRA reminds firms to verify the legitimacy of suspicious emails before responding, opening, downloading or previewing any attachments, or clicking on embedded links. Firms can report phishing campaigns to FINRA by contacting their Risk Monitoring Analyst, submitting a report to the FIFC or filing a regulatory tip.
FINRA has requested that the domain registrar and hosting provider suspend services for the known malicious domains.
Both the FBI and CISA urge you to promptly report phishing incidents to a local FBI Field Office, the FBI Internet Crime Complaint Center (IC3) at IC3.gov, or CISA via CISA’s 24/7 Operations Center ([email protected] or 888-282-0870).
For questions related to this Alert or other cybersecurity-related topics, contact the FINRA Cyber and Analytics Unit (CAU).
Note: This Alert does not create new legal or regulatory requirements or new interpretations of existing requirements, nor does it relieve firms of any existing obligations under federal securities laws, regulations, and FINRA rules. Member firms may consider the information in this Alert in developing new, or modifying existing, policies and procedures that are reasonably designed to achieve compliance with relevant regulatory obligations based on the member firm’s size and business model. Moreover, some information may not be relevant due to certain firms’ business models, sizes, or practices.
